Working at Moofwd

Software Engineer
Role Purpose
Moofwd, Inc. has a Software Engineer position in O’Fallon, MO.
Key Accountabilities
- Plan, design and develop modern microservice-based solutions using Java and Spring Boot in a cloud-based environment.
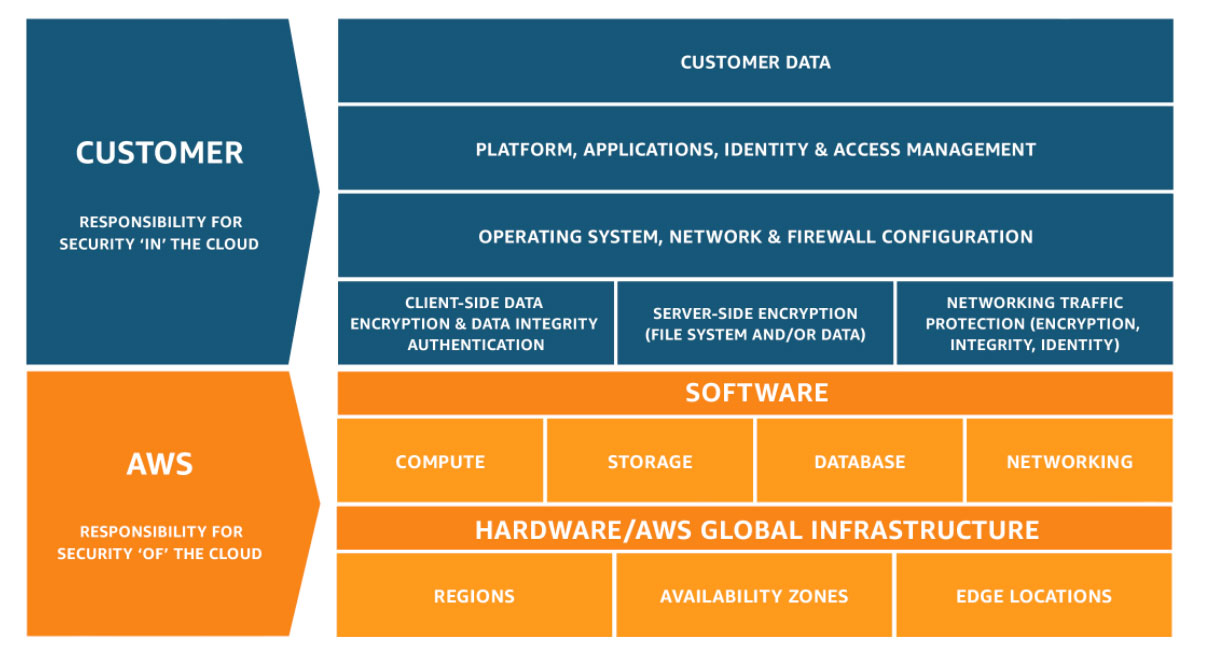
- Modernize Java applications for PAS micro-services architecture, twelve-factor app standards, services registration and discovery in Cloud, Cloud application security and reliability requirements.
Document and follow coding guidelines (e.g., branching, peer reviews, library use, logging, scanning rules, test-driven development, error handling).
Experience and Qualification
Master’s degree in Computer Science, Applied Computer Science or Computer Engineering and eight years of experience in software development required. Some experience with Linux administration, AWS Cloud, Azure Cloud, and Ansible Chef and Jenkins automation tools required.